I’m recruiting a PhD student. The funded opportunity is open to both UK (home) and international applicants, wishing to study on a full-time, on campus basis only.
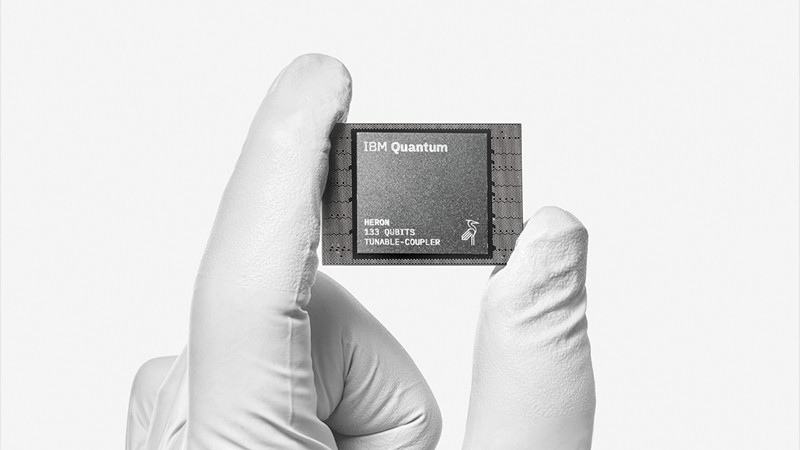
This ambitious project aims to contribute to the development of large-scale quantum communication infrastructure by identifying viable pathways for practical deployment of secure quantum networks. It investigates optical quantum repeaters for long-distance secure quantum key distribution (QKD). The PhD candidate will develop theoretical frameworks to analyse repeater architectures, evaluating both amplifier-enhanced and memory-assisted protocols. Crucially, you will develop experiment-ready models that rigorously account for realistic device imperfections—bridging the gap between theory and practical implementation.
Funding.
Both Home and International students can apply. Only home tuition fees will be covered for the duration of the 3.5-year award, which is £5,006 for the year 2025/26. Eligible international students will need to make up the difference in tuition fee funding (Band 2 for the year 2025/26). The student will receive a standard stipend payment for the duration of the award. These payments are set at a level determined by the UKRI, currently £20,780 for the academic year 2025/26.
Specific requirements of the candidate.
• First or upper second class (2:1) honours degree from a UK university or an equivalent qualification (or be close to completing) in Physics, Electrical Engineering, Computer Science, or a related discipline.
• Strong analytical and problem-solving skills, and the ability to work independently and collaboratively.
• Strong analytical skills and motivation for independent research are essential.
• Knowledge of optics and communications is desirable.
• Knowledge of quantum optics and quantum communications is desirable.
• Familiarity with programming (MATLAB, Python, etc.) is desirable.
How to apply.
Interested applicants should contact Dr Masoud Ghalaii (m.ghalaii@mmu.ac.uk) for an informal discussion.
To formally apply you will need to complete the online application form for a full time PhD in Computing & Digital Technology
Also, please complete the Doctoral Project Applicant Form, and include your CV and a covering letter to demonstrate how your skills and experience map to the aims and objectives of the project, the area of research and why you see this area as being of importance and interest. Please upload these documents in the supporting documents section of the University’s Admissions Portal.
Closing time.
27th February 2026




You must be logged in to post a comment.